Database Security Guidelines
Database Security Guidelines - New car reviews provide useful insights for buyers wanting to make well-researched decisions. They showcase the newest models, presenting their design, features, driving capability, and technology. By covering various aspects, such as mileage, comfort, and safety scores, reviews help potential owners compare vehicles effectively.
In-depth reviews also include test drive feedback and expert opinions to give a practical view. They often discuss pricing, trim options, and warranty details to guide buyers toward the best choice. With regularly updated reviews, enthusiasts and consumers can keep updated about developments and advancements in the automotive industry.
Database Security Guidelines
Database Security Guidelines
Invalid prisma workspaces create invocation The column similarityThreshold does not exist in the current database Prisma Schema 为什么MySQL输入命令后显示“No database selected ”? 关注者 13 被浏览
vscode clangd

App Store Security Guidelines For Approving Apps ITIGIC
Database Security Guidelineswolai的database(数据表格)已经上线,值得入手吗? 昨晚(2021年11月14日)wolai宣布database开始公测,我试用了一下觉得完成度很可以,目前在用的笔记有印象笔记和飞书文 … May 28 2023 nbsp 0183 32 Andy 15445 15645Intro to Database Systems
先重装无法解决, 然后试了官网给的解决方案,“去官网搜索Problem Accessing the Database When Launching Multisim ” 它给了两个方法:删除文件 和 处理注册表都不行。 25年10月27日 … Oracle Acquires British Database Security Firm What Is Data Security Oracle
MySQL No Database Selected

ASP NET CORE API Security Guidelines Be Careful With Your Predictable
Nov 12 2025 nbsp 0183 32 1 XPS 1 XPS X ray IT Security Guidelines
Access Microsoft Office Access Access Access Is Your Data Secure 13764045638 QQ 47079569 Network Security Database Vulnerabilities Coursera

DataBase Security Notes And E Books Raghu
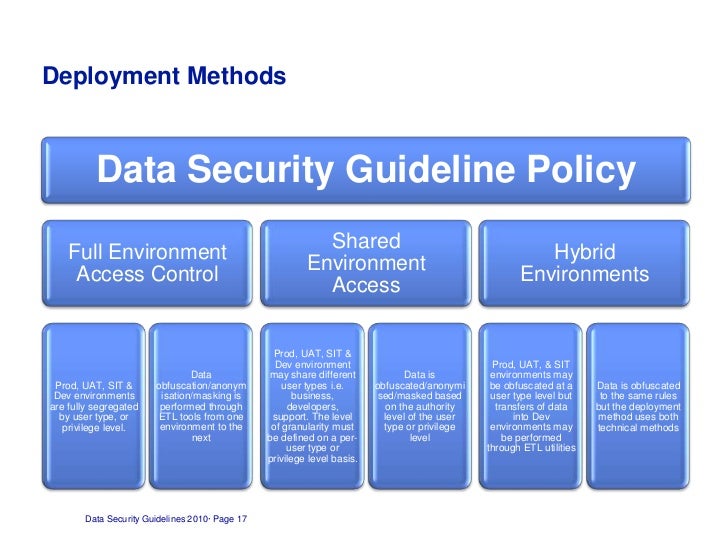
Data Security Guidelines

From The Equifax Hack To The Blockchain Online Database Security Is
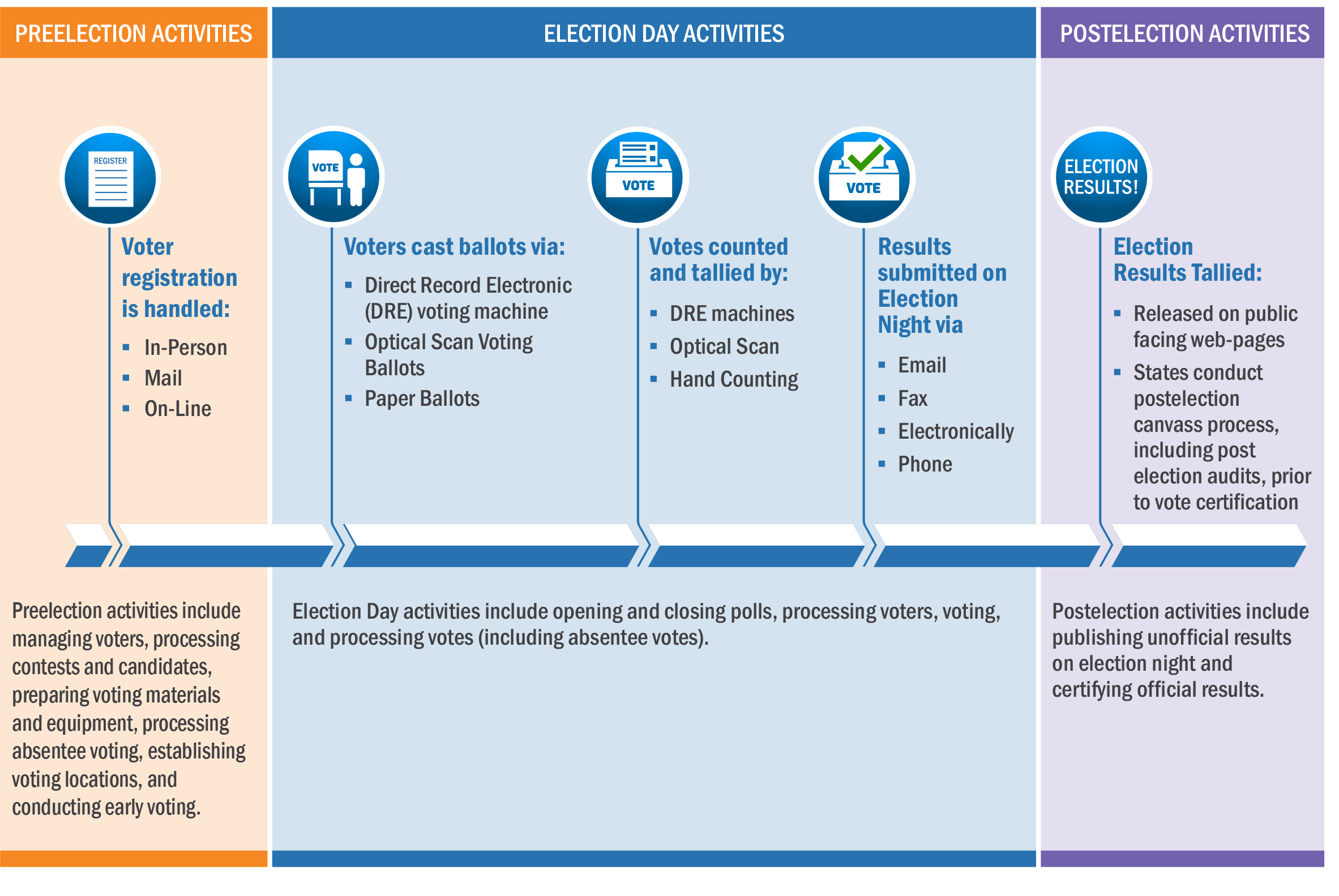
To Help Protect Our Elections NIST Offers Specific Cybersecurity
Database Security For Cyber Professionals AvaxHome
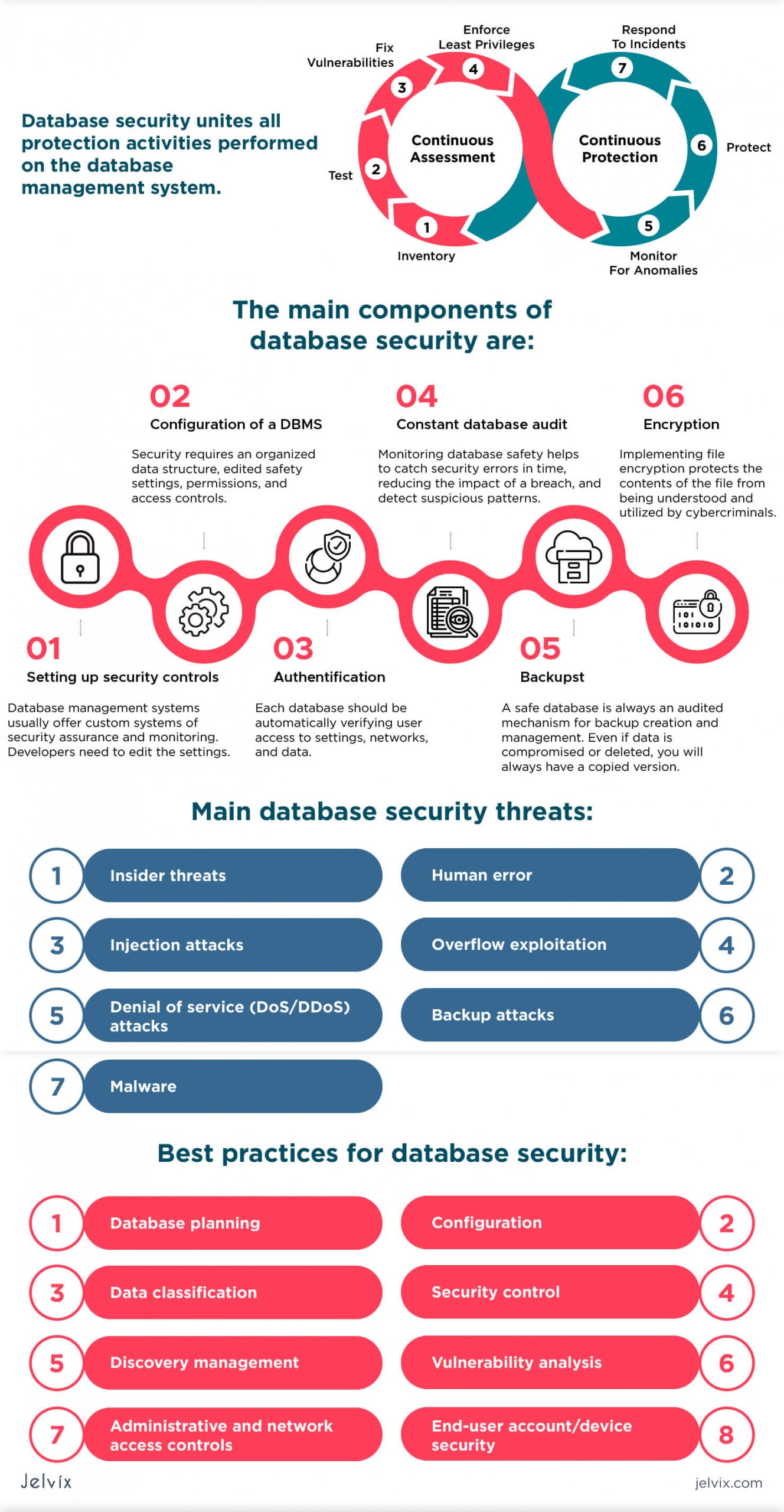
What Is Database Security Standards Threats Protection

Obtaining A Security Clearance National Security Clearances
IT Security Guidelines
What Is Database Security Standards Threats Protection
ISMS DOC A06 3 Information Security Guidelines For Project Management