Database Security Best Practices
Database Security Best Practices - New car reviews provide valuable insights for buyers looking to make smart decisions. They feature the latest models, presenting their design, features, driving capability, and tech. By covering various aspects, such as fuel efficiency, comfort, and safety ratings, reviews help potential owners evaluate vehicles effectively.
In-depth reviews often feature driving impressions and expert opinions to give a practical view. They often discuss pricing, variants, and warranty details to guide buyers toward the best choice. With regularly updated reviews, car fans and consumers can stay informed about trends and advancements in the automotive industry.
Database Security Best Practices

Database Security Best Practices
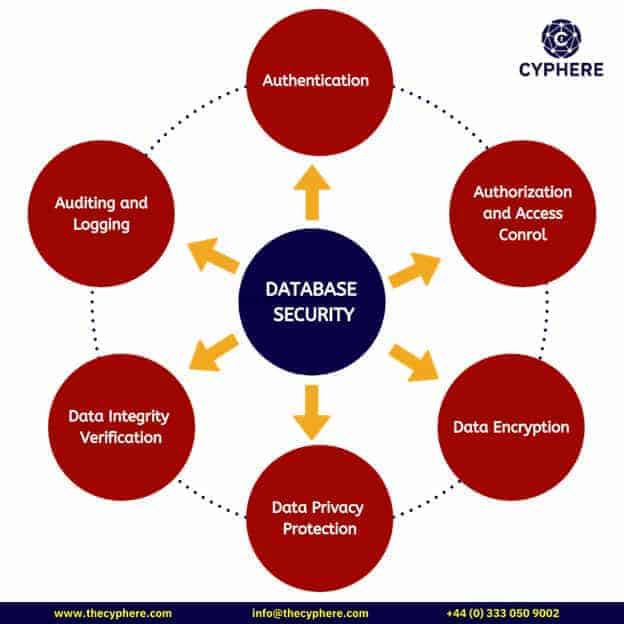
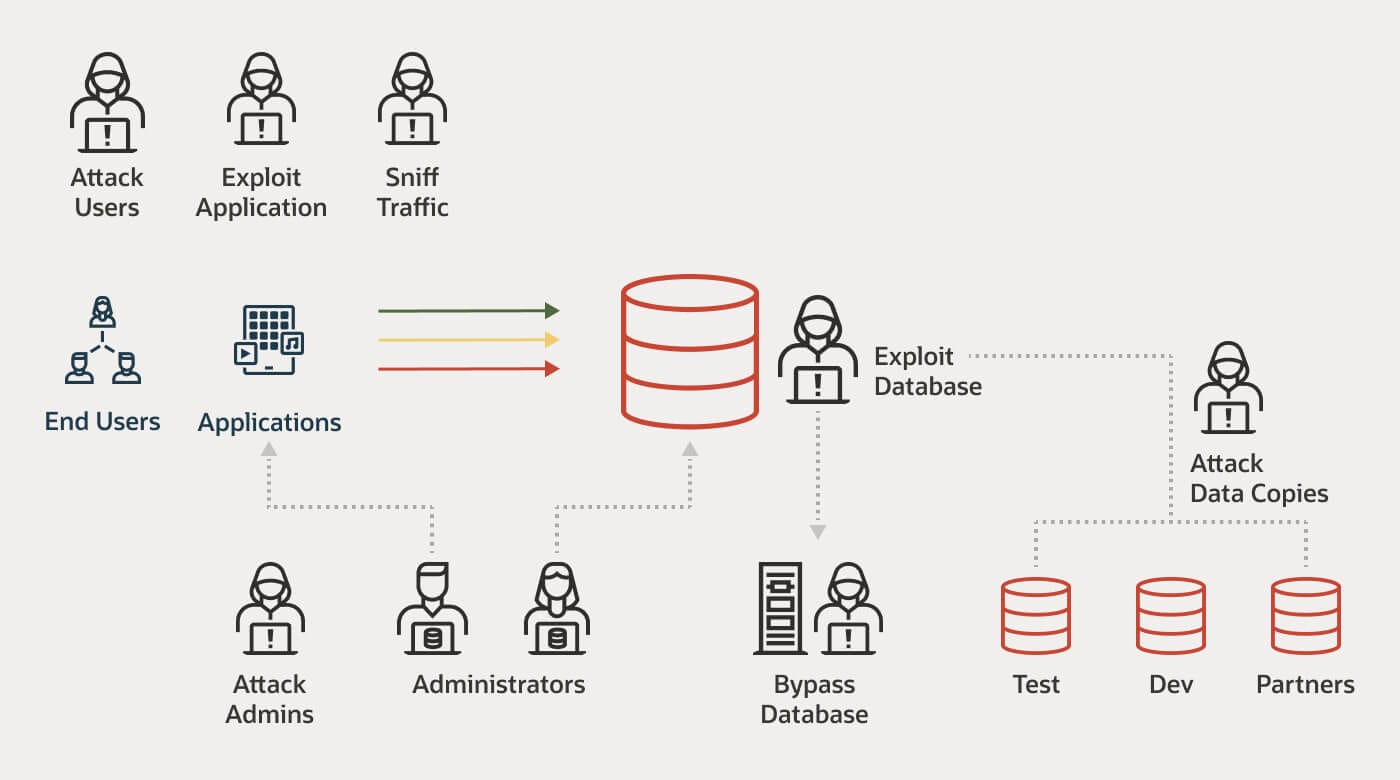
Web Best practices Because databases are nearly always network accessible any security threat to any component within or portion of the network infrastructure is also a threat to the database and any attack impacting a user s device ;Database security is the practice of protecting files within a database from accidental and malicious threats. This subset of cybersecurity covers all the tools and measures teams use to: Prevent unauthorized access to files. Maintain data integrity. Ensure data stays available to users and apps.
Database Security Best Practices The Essential Guide
Database
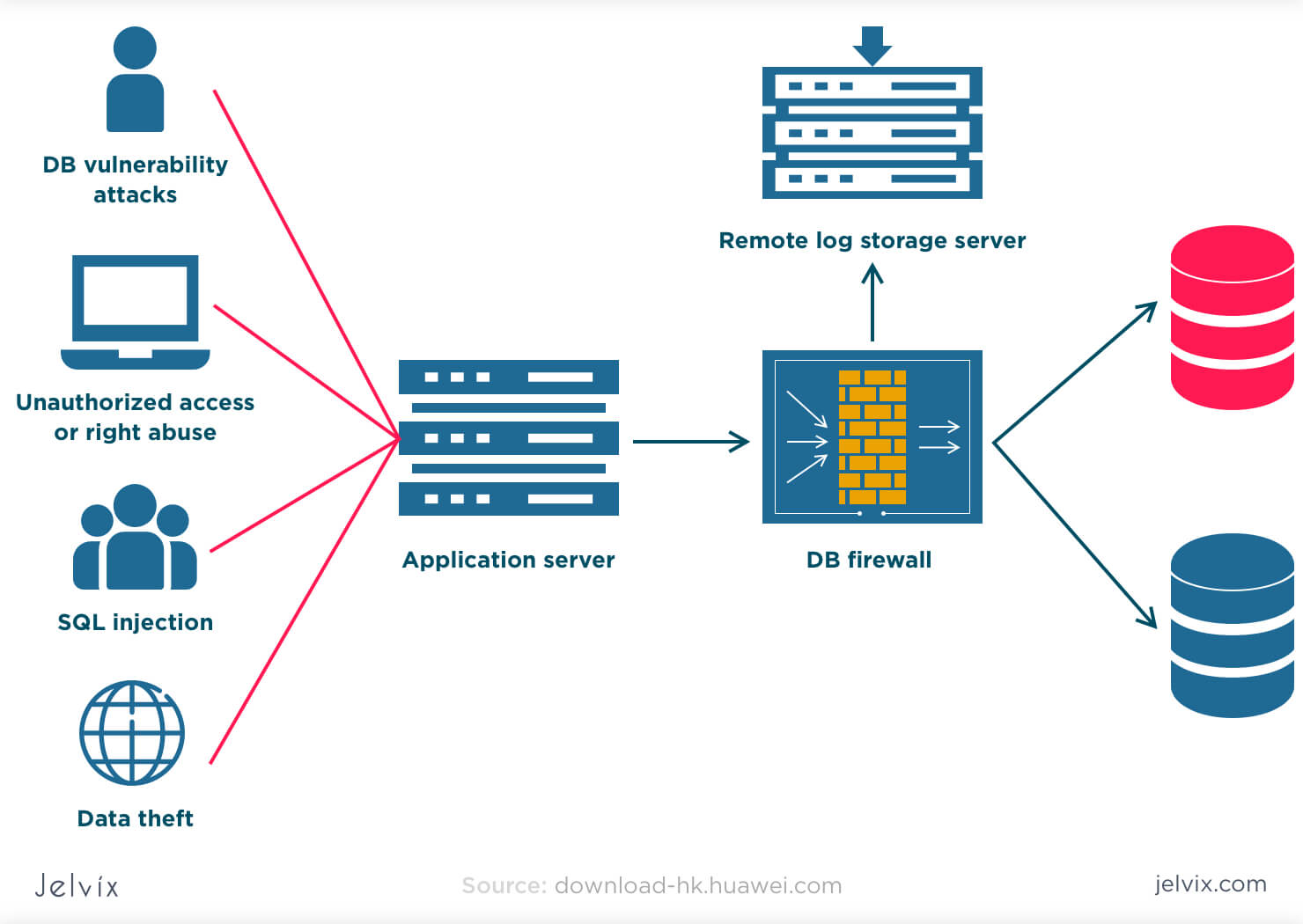
Database Security Best Practices;1. Deploy physical database security Data centers or your own servers can be susceptible to physical attacks by outsiders or even insider threats. If a cybercriminal gets access to your physical database server, they can steal the data, corrupt it or even insert harmful malware to gain remote access. Web Apr 21 2023 nbsp 0183 32 7 Database Security Best Practices 1 Separate Database Servers By definition web servers must be publicly accessible to be used but this also paints 2 Use Database Firewalls Databases only become useful if accessed but that access must be protected The first layer 3 Secure Database
Authentication The database should be configured to always require authentication, including connections from the local server. Database accounts should be: Protected with strong and unique passwords. Used by a single application or service. Configured with the minimum permissions required as discussed in the permissions section below. Database Security Best Practices Stealthbits Database Security Best Practices Simple Worthwhile Concepts Part
What Is Database Security Common Threats And Best Practices
What Is Database Security Security Best Practices Tips
Web Aug 2 2022 nbsp 0183 32 4 Encrypt sensitive data Encryption is a database security best practice no brainer Use strong encryption to protect databases in three ways Require all database connections use TLS encryption to protect data in transit Encrypt disks containing data stores to protect against their loss theft or improper disposal 6 Best Practices For Data Security In The Cloud Infographic LightEdge
Web Dec 1 2023 nbsp 0183 32 Database Security Best Practices Here are several best practices you can use to improve the security of sensitive databases Actively Manage Passwords and User Access If you have a large organization you must think about automating access management via password management or access management software Master Data Privacy Best Practices To Protect Your Business Oracle Database Security Best Practices DNSstuff
Por Qu Es Necesario Un Firewall De Base De Datos

What Are The Different Database Rkimball

Database Security Best Practices

Data Loss Prevention DLP Best Practices To Strengthen Your Data

7 Database Security Best Practices CyberCureME

Database Security Best Practices Short Guide CodeIT
6 Database Security Best Practices
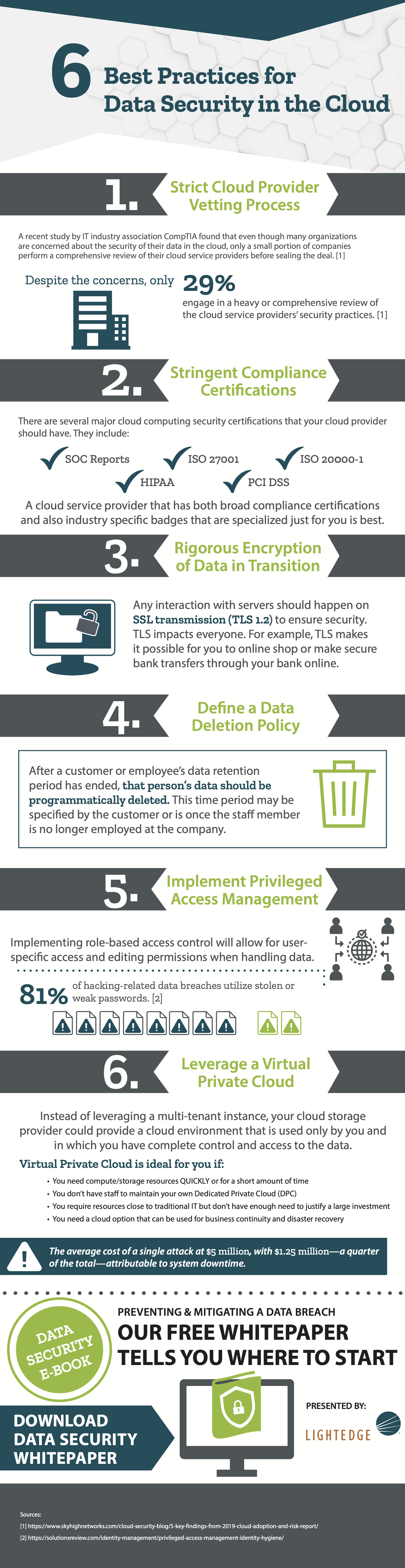
6 Best Practices For Data Security In The Cloud Infographic LightEdge
Database Security Best Practices 2022
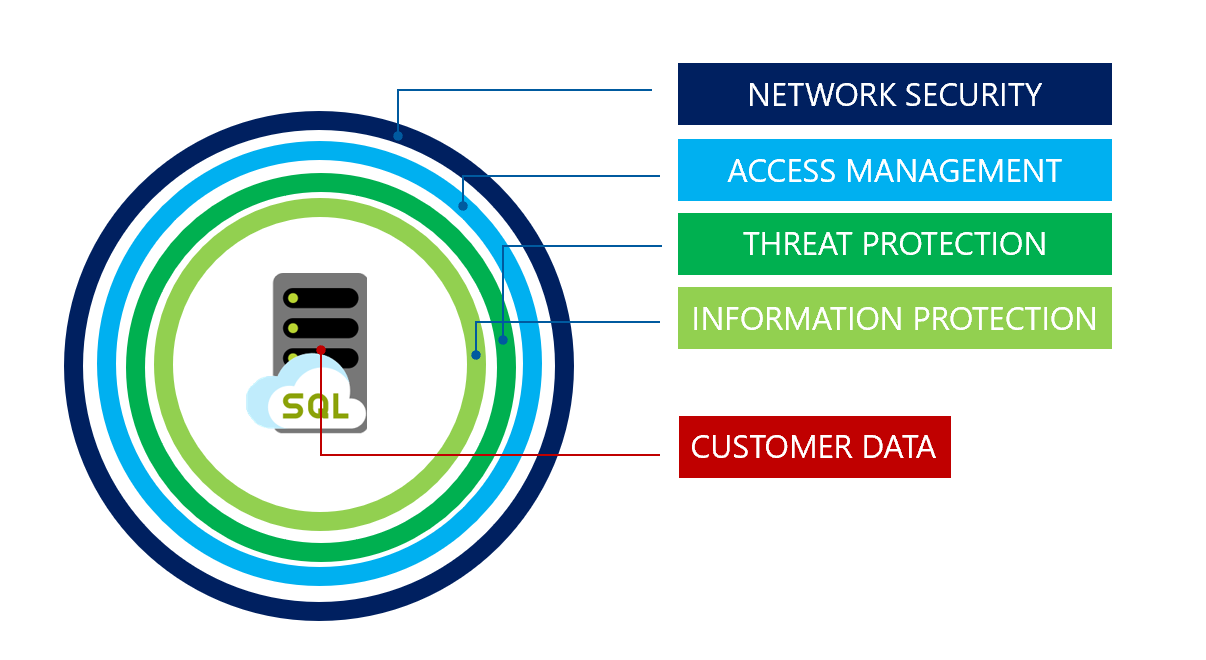
Security Overview Azure SQL Database Azure SQL Managed Instance
